It can be easy to measure the financial impact of IT investments that reduce hardware, licensing, trunking or labor costs. But determining the return on investment (ROI) from cybersecurity measures can be much more challenging. How do you show the financial benefits of preventing a breach or a ransomware attack?
A team of cyber security experts addressed that issue in a recent BrightTalk session, “Proving Security Effectiveness to Your CISO, CFO and Board.” Brian Contos, CISO and vice president, technology innovation. Mandiant Security Validation, led a discussion with Ryan Dodd, founder and CEO, Cyberhedge, and Major General (Retired) Earl Matthews, Mandiant’s vice president of strategy and a former CISO for the U.S. Air Force.
“The question of validation is difficult with cybersecurity because the technology is invisible to the organization, unlike the sales team, which can always show its numbers,” said Dodd.
Focus on risk
Therefore, one of the best strategies for demonstrating value is to focus the conversation on risk, and communicate in dollar-based terms. “Instead of looking at security as a binary outcome – attacks vs. prevention – you should take a more nuanced approach, said Matthews. “Think about how good security can improve the overall performance of the company.”
Contos added that senior leadership and board members may not stay current with technology trends, but they do understand risk. “If you can show the security gaps that need to be addressed, such as devices or processes that need to be improved through IT investments, they can make an educated business decision,” he said.
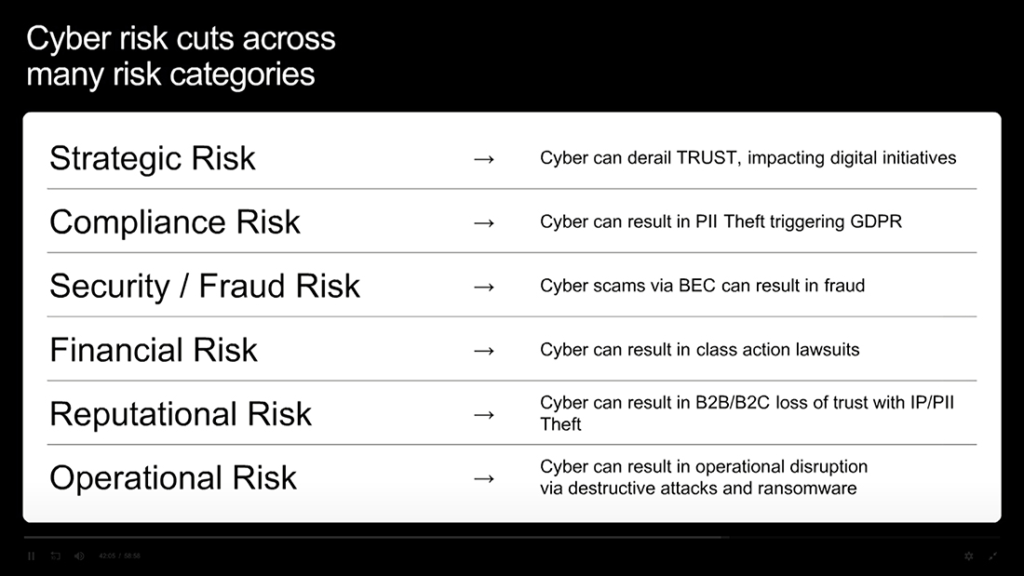
Matthews noted that there are multiple types of risks from cyber attacks, including financial, compliance and reputational issues. “Ransomware, in particular, can shut things down and have a direct impact on operational performance,” he added.
Therefore, IT leaders should continuously monitor the threat landscape, and the organization’s risk profile, including remote workers, business partners, vendors and IoT sensors and devices for vulnerabilities.
Due to the importance of technology in driving business value, some companies have called off planned acquisitions rather than take on the high risks associated with an insecure infrastructure or the expenses needed to rebuild the system, Matthews said.
Assessing relative performance
Along with quantifying cybersecurity risks from an inside perspective, it is now possible to gain a third-party assessment showing how well organizations are doing compared to their peers.
Dodd outlined Cyberhedge’s proprietary system for rating more than 5,000 publicly traded companies on cyber governance. The top 20 percent receive a 5-star rating and the lowest 20 percent receive only one star, with the results independently validated. The 5-star companies have outperformed the financial averages across all major developed markets, he said.
Last year, the gap between 1-star and 5-star companies was particularly apparent, as organizations relied more heavily on their digital assets to serve customers, Dodd said. “Even the boring consumer goods companies that figured out digital are beating the competition,” he said. “That hold true across every sector, which makes sense because technology is driving so much of the value in the business.”
Dodd added that companies like SolarWinds were listed as high risk, well before they reported major security breaches. The telltale signs might include operational redundancies, relatively low productivity and higher operational costs.
To summarize, an effective way to prove the value of cybersecurity measures includes ongoing internal monitoring and actions, complemented by an outside assessment. But most importantly it means focusing on business risks, rather than the latest cyber tools. “You have to validate your actions in terms of dollars,” said Dodd. “Show how your IT investments will lower the risks and have a positive impact on financial performance.”
I’ve been absent for some time, but now I remember why I used to love this site. Thanks , I will try and check back more often. How frequently you update your site?