Phil Quade believes in taking a scientific approach to cybersecurity. “Just as there’s no sense trying to fight the laws of physics, a cybersecurity strategy should be based on science,” he said. “That means focusing on the elements of speed and connectivity.”
Quade is the chief information security officer (CISO), Fortinet, and author of “The Digital Big Bang: The Hard Stuff, the Soft Stuff, and the Future of Cybersecurity.” He gave a fireside chat on “The Science of Cybersecurity: Best Practices in the New Normal,” in a recent BrightTalk webinar with Theresa Lanowitz, director, AT&T Cybersecurity.
Kicking off the discussion, Lanowitz called cybersecurity a journey, rather than a destination. “We try to solve it one problem at a time.” Quade agreed, adding that cybersecurity requires a team approach that includes line-of-business leaders. After all, no one wants cybersecurity to slow down speed and performance.
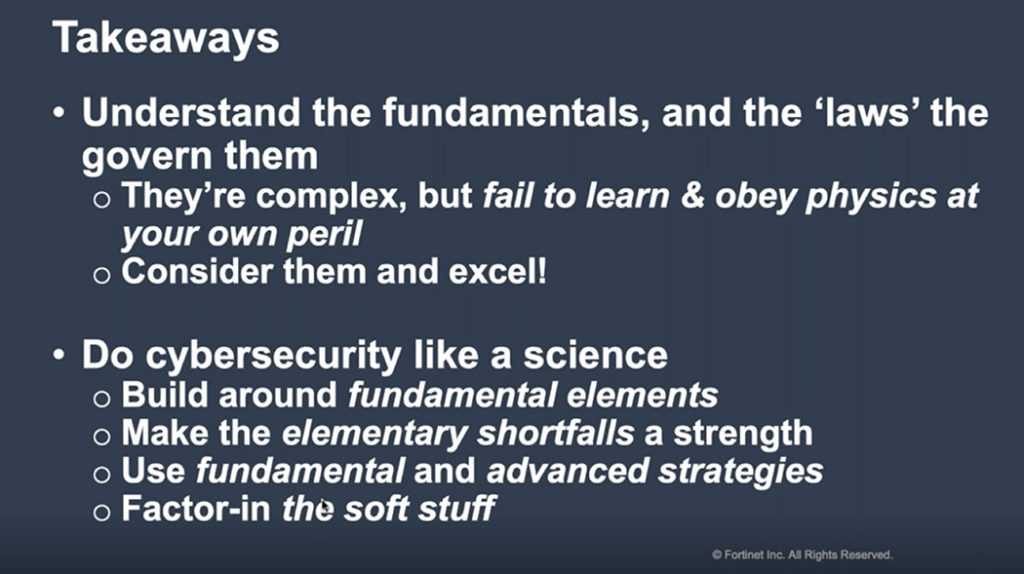
Quade then outlined four pillars of a scientific approach to cybersecurity. “You should build your architecture on these strategies,” he said. “Otherwise, you have to lurch from technology to technology.”
Elementary shortfalls
Quade’s first cybersecurity pillar was elementary shortfalls: authentication, patching and training. “Lack of authentication is the root cause of nearly all cybersecurity problems,” said Quade. “If you can solve the issues involving people, processes and data, you will be ready to move on to bigger problems like world peace!”
As for patching, Quade said lack of computer and network hygiene has been a persistent problem since the early 1980s at least. “Too many times, we hurt ourselves by not staying current with operating systems and applications,” he said.
Quade also stressed the importance of training users in the basics of security. Too many organizations don’t appreciate the importance of instilling awareness of threats like malware and identity theft, he added.
“These types of fixes are relatively straightforward,” he said. “You need to keep upgrading your systems, though, because that makes an attacker’s job more difficult.”
Fundamental strategies
Next, Quade highlighted three fundamental strategies of cybersecurity: segmentation, access control and cryptography. For instance, segmentation on a micro and macro level – also called a zero trust approach – can limit the penetration ability of an attacker. “Agile segmentation also allows you to enter business partnerships and share a piece of your data,” he added.
Access control involves ensuring that a user can see certain data sets but not others unless authorized. This approach, which is similar to authentication, helps protect sensitive data.
Quade called cryptography “the only silver bullet in cybersecurity,” as a single message the right encryption can’t be broken by brute force. “However, you want to find the right level of granularity to optimize performance as well as speed and security.”
Advanced strategies
Advanced cybersecurity strategies include visibility, inspection and failure recovery, according to Quade. “You can’t defend what you can’t see,” said Quade. “So you need to identify threats quickly and understand the context.”
Inspection involves SSL decryption in order to identify nefarious activity in the network. This might involve insiders, as well as outside attackers, Quade said. As for failure recovery, organizations should look for automated resiliency. “The availability of cloud resources will help detect weak conditions and automatically take action,” he said.
High-order dimensions
Quade’s fourth pillar was high-order dimensions: human frailty, complexity management and privacy. “We all need to address the human part of the cybersecurity equation, including complexity management,” he said. “We get tired and miss things, or we might not have received adequate training on the latest technology.”
While bolstering cybersecurity, organizations also need to protect data privacy. “We need to do privacy at speed and scale, just like our security tools,” Quade said.
After his presentation, Quade was asked how to make cybersecurity more than an afterthought in an organization. “You need to approach it as an enabler of business, rather than as a cost center,” he said. “It allows you to operate more effectively, particularly when users are working from home. Treat cybersecurity as a science and emphasize the lift it can provide rather than creating a drag on your business.”